Enhancing cloud data security using quantum key distribution (QKD) and quantum cryptography
Keywords:
Quantum Cloud Security, Post-quantum cryptography (PQC), Quantum key distribution (QKD), Hybrid cryptography, TLS handshake performanceAbstract
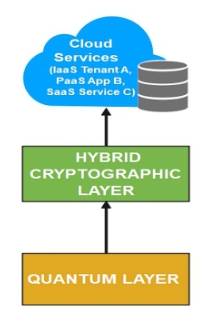
Cloud computing systems face serious security risks that are intensified by advances in quantum computing because powerful quantum algorithms such as Shor's algorithm can break widely used public-key schemes which include RSA and ECC. The cloud environment needs Post-Quantum Cryptography (PQC) and Quantum Key Distribution (QKD) as countermeasures but their individual deployment creates problems because scalability and infrastructure requirements become obstacles for multi-tenant systems. This research proposes a hybrid security architecture that uses both hardware-based QKD for symmetric key generation over optical fibers and PQC for authentication through quantum-resistant key encapsulation using CRYSTALS-Kyber and digital signatures with CRYSTALS-Dilithium. The hybrid design uses XOR to combine the QKD-generated secret with the PQC-derived key material which creates the final session key yet security remains intact if either component gets compromised. The system tested on a private cloud testbed with 10 virtual machines and a 50 km commercial QKD link through optical fiber measured performance against Classical TLS 1.3 and PQC-TLS and QKD-only configurations. The results showed that QKD-only achieved the lowest handshake latency of 5.2 ms while the hybrid approach delivered the strongest security through a 19.8 ms overhead which was only 1.7 ms slower than pure PQC. After creating the secure channel all systems achieved similar data throughput of about 942 Mbps which shows that quantum-security mechanisms affect the connection setup phase instead of persistent data transfer.
Published
How to Cite
Issue
Section
Copyright (c) 2026 O. Sarjiyus, Umaru Faruku Adamu, Salamatu Umar (Author)

This work is licensed under a Creative Commons Attribution 4.0 International License.